Modern supply chains no longer run on phones, emails, and paper logs. They depend on digital platforms, real-time tracking, shared dashboards, APIs, and partner portals to move goods efficiently.
When these systems work, operations feel smooth and predictable.
When they fail even for a few hours the supply chain feels blind and unstable.
That’s why cyber attacks today are not just IT incidents.
They are supply chain incidents.
A cyber attack can:
- Stop shipment updates from flowing
- Break integrations with carriers and vendors
- Show wrong inventory or ETA data
- Force teams back into manual coordination
The result is not just “system issues.”
It’s missed deliveries, delayed decisions, higher costs, and lost trust.
In a digitally connected environment, operations move at the speed of data.
When cyber incidents disrupt that data, physical supply chains slow down immediately.
This shift is critical for leaders to understand:
Cyber risk = operational risk.

📌 The Real Operational Impacts of Cyber Attacks (What Leaders Actually Feel)
Cyber attacks rarely announce themselves as “security problems.”
For operations leaders, they show up as confusion, delays, and constant firefighting.
Below are the most common impacts and how they appear in real operations.
1️⃣ Shipment Delays and Exception Backlogs 🚚
When systems are disrupted, shipments don’t stop instantly but they slow unevenly.
What it looks like on the ground:
- Orders move, but confirmations lag
- Exception queues grow faster than teams can clear them
- Manual approvals and overrides increase
- Delivery promises quietly slip
The delay isn’t always caused by trucks stopping it’s caused by decisions slowing down.
2️⃣ Tracking Failures and Loss of Real-Time Visibility 👀
Real-time tracking is the control center of modern supply chains.
Cyber incidents often break this visibility first.
What it looks like on the ground:
- Dashboards stop updating correctly
- Shipment milestones disappear or lag
- Control towers show partial data
- Teams rely on calls, emails, and guesses
Without visibility, leaders can’t prioritize actions confidently.
Real-time tracking is crucial in modern supply chains, and when cyber incidents disrupt this visibility, it can cause massive operational delays. Explore how blockchain can help prevent such disruptions by providing secure, transparent, and immutable transaction records.
3️⃣ Data Manipulation (Wrong Orders, Wrong Routes, Wrong Inventory) ⚠️
Some cyber incidents don’t shut systems down they quietly change data.
What it looks like on the ground:
- Inventory numbers don’t match physical stock
- Orders route to the wrong location
- Replenishment triggers fire at the wrong time
- Planners chase problems that aren’t real
Operations continue but on false information, which is often worse than no data.
4️⃣ Partner / Vendor Access Issues (Compromised Credentials, Locked Portals) 🔐
Supply chains depend on shared access across partners.
What it looks like on the ground:
- Vendors suddenly can’t log in
- Carrier updates stop mid-shipment
- Portals are locked as a precaution
- Teams switch to manual coordination
Even if internal systems are fine, partner access failures break flow.
5️⃣ System Downtime (TMS/WMS/Portals/APIs Stop = Operations Stop) ⛔
When core platforms go down, operations slow immediately.
What it looks like on the ground:
- TMS or WMS unavailable for hours
- API connections to carriers fail
- Customer portals show errors
- Teams pause actions to avoid mistakes
In digital supply chains, system downtime = operational downtime.
📌 A Realistic Scenario Using a Modern Platform Like ShipChain
To see how cyber incidents turn into operational disruption, let’s walk through one realistic day inside a digitally connected supply chain.
This is not a worst-case breach.
It’s a normal business day that slowly goes wrong.
🔹Morning: Small, Easy-to-Ignore Signals ☕
The day starts quietly.
- A few shipment statuses update late
- One partner reports portal login issues
- A dashboard refresh takes longer than usual
Operations teams using a modern platform like ShipChain where real-time visibility and integrations are central notice the friction early, because data flow equals operational flow.
Nothing looks broken yet, so work continues.
🔹Midday: Integrations Begin to Fail 🔌
By midday, API connections with carriers start timing out.
- Shipment updates stop flowing automatically
- Partner systems fail to sync
- Manual status checks increase
In environments built around real-time data and shared visibility, like Shipchain, these integration failures immediately slow decision-making.
Teams can still operate but with uncertainty.

🔹Afternoon: Exceptions Explode 📈
As the day progresses:
- Exception queues spike
- Customer ETAs become unreliable
- Support teams field “where is my order?” calls
- Operations managers manually verify data
Different teams now firefight the same underlying issue without a single clear view of what’s happening..
🔹Result: Delays, Cost, and Trust Damage 💸
By end of day:
- Shipments are delayed
- Labor costs increase due to manual work
- Dashboards lose credibility
- Partners and customers lose confidence
The cyber incident didn’t just affect systems.
It disrupted the flow that keeps the supply chain running.
📌 Why These Attacks Happen So Easily in Digital Supply Chains
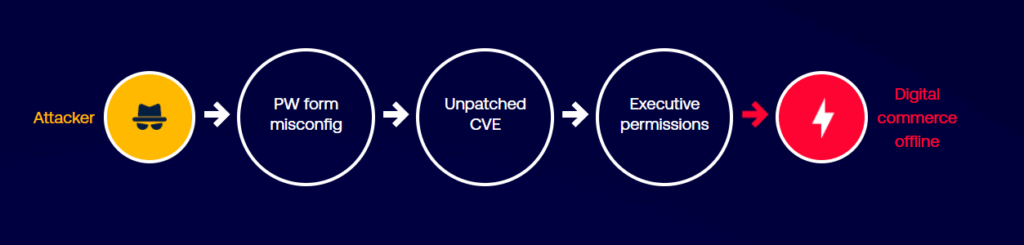
Digital supply chains are built for speed. Cloud platforms, partner portals, real-time tracking, and API connections help teams move faster and make better decisions. But that same speed creates more openings for disruption. Most cyber incidents in operations don’t happen because a company is careless. They happen because modern supply chains have many moving parts, and a few small gaps are enough to cause a real operational breakdown.
1. Misconfigured Cloud Services ☁️
Cloud systems are powerful, but they are also easy to expose by mistake. One wrong setting can make a portal, storage location, or service accessible in a way it was never meant to be. These mistakes often happen during fast deployments, urgent integrations, or “temporary access” changes that don’t get reversed. Everything looks normal until attackers discover that open door.
2. Unpatched Systems 🔧
Supply chains run on systems that teams don’t want to touch because downtime is expensive. Updates get delayed because operations can’t afford disruption during peak cycles. But attackers actively look for known weaknesses that already have public fixes available. When patching is delayed for weeks or months, it becomes less of a technical issue and more of an operational risk waiting to happen.

3. Exposed Internet-Facing Assets 🌐
Many supply chain systems must be reachable from outside. Tracking dashboards, customer portals, vendor logins, and APIs exist specifically so partners can connect. The problem is that anything reachable from the internet can be scanned, tested, and targeted. This doesn’t mean “don’t expose systems.” It means the exposure has to be understood, controlled, and monitored or the supply chain becomes easy to disrupt.
4. Risky Third-Party Integrations 🔗
A digital supply chain is not one company’s system. It’s a network. Carriers, 3PLs, suppliers, and marketplaces connect through integrations that move data automatically. Every integration increases the number of ways something can break. Even if your internal environment is strong, a weaker partner connection can trigger failures that spread across shared workflows, portals, and data flows.
5. Weak Identity and Access Controls 🧾
Operations teams need fast access, so accounts and permissions often grow messy over time. People switch roles, vendors rotate staff, and old access doesn’t always get removed. Shared credentials and over-permissioned accounts are common in partner-heavy environments. During an incident, weak access control makes it easier for disruption to spread and harder to isolate the problem quickly.
The main point is simple: supply chains become easy to attack because they are designed to be connected. The more connected they are, the more they rely on visibility, integrations, and shared access and those are exactly the areas attackers aim to disrupt.
“To protect your infrastructure from these devastating cyber attacks, using industry-leading tools is essential. You can secure your network today and save on costs by using a Tenable coupon code to get started with professional-grade protection.”
📌 How Exposure Management Helps Reduce These Disruptions (Tenable Context)
Most supply chain disruptions from cyber incidents happen because teams don’t see risk early enough. Systems look fine until tracking stops, portals fail, or integrations break.
Exposure management helps by making digital risk visible before it affects operations.
1️⃣ Seeing What Could Break Operations 🔍
Supply chains rely on many exposed systems dashboards, APIs, partner portals, and cloud services. Exposure management helps organizations understand which of these are visible to the internet and which ones matter most to daily operations. Fewer unknowns means fewer surprise outages.
2️⃣ Focusing on Risks That Cause Downtime ⚠️
Not every weakness leads to disruption. Some issues can safely wait; others can stop shipments or visibility. Exposure management helps prioritize the risks that could actually interrupt supply chain flow, so teams focus on what matters operationally.
3️⃣ Reducing Cloud and Integration Failures ☁️
Misconfigurations and weak points in cloud services, web apps, and APIs are common causes of outages. Exposure visibility helps spot these early, reducing the chance of tracking systems, portals, or integrations going down during critical periods.
Platforms such as Tenable are often referenced as industry examples of how organizations approach exposure management across modern digital environments.
In short, exposure management doesn’t just improve security it helps keep supply chain operations running smoothly.
📌 Practical Playbook for Supply Chain Leaders (Non-Technical)
- ❓ Know which supply chain systems are exposed to the internet, especially tracking dashboards, portals, and APIs.
- ❓ Ensure teams know how to isolate affected systems quickly without shutting down everything.
- ❓ Identify which systems and integrations would stop operations if they were disrupted.
- ❓ Make sure there is a backup plan when real-time visibility goes down, so teams are not forced to stop work.
- ❓ Review partner and vendor access regularly to avoid confusion during incidents.
- ❓ Avoid shared or over-permissioned accounts that make problems spread faster.
- ❓ Define clear escalation paths so operational decisions are not delayed during an incident.
- ❓ Treat cyber preparedness as part of operational risk management, not just IT security.

📌 Operational Confidence Comes from Visibility + Preparedness
Cyber attacks now hit supply chains where it hurts most: daily operations. They cause delayed shipments, lost visibility, wrong decisions, and stressed partner relationships. The issue is not just system failure, but loss of control at critical moments.
As supply chains rely more on digital platforms and integrations, resilience depends on knowing what could break and being ready when it does.
Visibility into operations and exposure reduces surprises and limits damage.
In today’s environment, cyber resilience is supply chain resilience. Leaders who plan for disruption protect performance, trust, and continuity.
“Related Article”
- How ShipChain Accounting & Tenable Build Finance Confidence
- Supply Chain Operational Confidence in Digital Logistics
📌 FAQs
1. How do cyber attacks impact supply chain operations?
They disrupt tracking, delay shipments, break integrations, and increase operational errors.
2. Why should supply chain leaders care about cybersecurity?
Because cyber incidents directly affect delivery timelines, costs, and customer trust.
3. What is supply chain visibility disruption?
When real-time tracking data becomes unavailable or unreliable during an incident.
4. How does exposure management reduce disruption?
By identifying risks that could cause operational downtime before they escalate.
5. Are third-party integrations risky?
Yes. Shared access and integrations increase exposure and potential disruption.