Looking for a clear, honest breakdown of Tenable? 🚀 You’re in the right place. This review is built to guide you step-by-step so you can quickly understand how Tenable works, what it offers, and whether it truly fits your security needs.

We won’t waste your time with buzzwords. Instead, you’ll see real features, real pricing insights, and real use cases that help you decide with confidence.
Ready to see if Tenable review is actually worth your attention and your budget? 🔐
Let’s dive in and find out. 👇
1️⃣ What is Tenable?
In simple words, Tenable is a cybersecurity platform designed to find and fix security weaknesses before hackers do. Instead of reacting after an attack happens, Tenable helps organizations stay proactive by continuously monitoring their digital environment for vulnerabilities.
At the core of Tenable’s ecosystem is its globally trusted vulnerability scanner, Nessus, which security professionals use to detect misconfigurations, missing patches, and exploitable risks across systems and networks. 🛡️
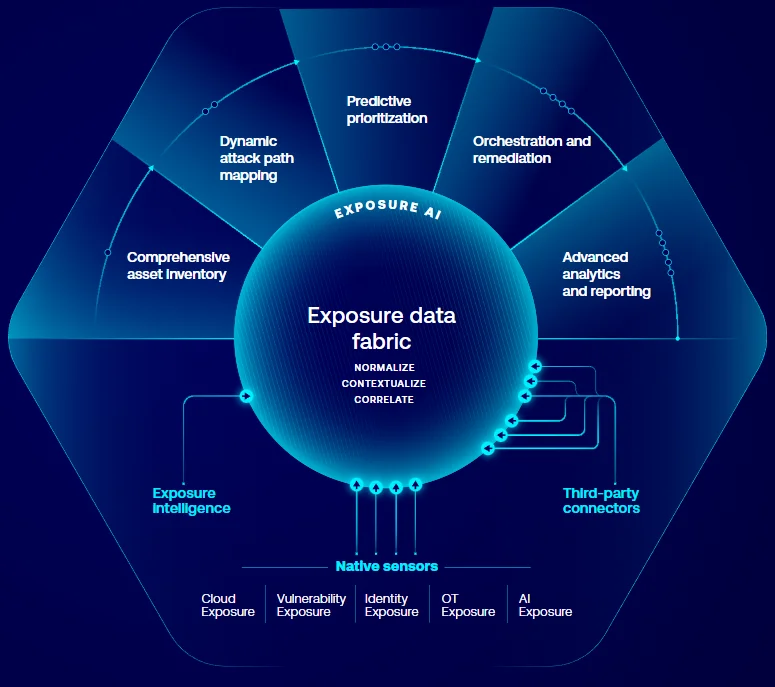
But Tenable isn’t just about scanning anymore. Over the years, it has evolved into a complete cyber exposure management platform giving visibility across IT assets, cloud workloads, identities, web apps, and even industrial systems.
👉 Why this matters:
Modern cyber threats don’t target just servers they target everything connected. Tenable helps organizations see their entire attack surface in one place.
💡 In Short:
- Finds vulnerabilities automatically
- Prioritizes risks based on real threat data
- Helps teams fix issues faster
- Works across cloud, hybrid, and on-prem environments
That’s why Tenable is trusted by enterprises, governments, and security teams worldwide. 🌐
🔑 Main Features of Tenable
1️⃣ Vulnerability Management 🔍
This is the core foundation of Tenable’s platform.
Tenable continuously scans your systems, networks, and applications to detect security weaknesses before attackers can exploit them. It identifies known vulnerabilities (CVEs), outdated software, missing patches, and risky configurations.
Instead of running occasional scans, Tenable provides continuous vulnerability monitoring, ensuring new risks are detected the moment they appear.
👉 Why this matters:
Cyber threats evolve daily. Without continuous scanning, organizations remain exposed without even realizing it.
2️⃣ Continuous Asset Discovery 🖥️☁️
Tenable automatically discovers and inventories every asset connected to your environment.
This includes:
- Laptops & endpoints
- Servers & databases
- Cloud workloads
- Containers
- IoT devices
- OT systems
You get a complete, real-time inventory of your digital infrastructure.
👉 Why this matters:
You can’t secure assets you don’t know exist. Asset discovery eliminates hidden attack surfaces.
3️⃣ Exposure Management Platform 📊
Through Tenable One, organizations get a unified view of their entire cyber exposure.
Instead of seeing vulnerabilities in isolation, Tenable combines:
- Vulnerabilities
- Identity risks
- Cloud misconfigurations
- Web app exposures
- OT risks
All of this appears in one consolidated dashboard with exposure scoring.
👉 Why this matters:
Security becomes strategic. Teams understand overall risk posture not just isolated issues.
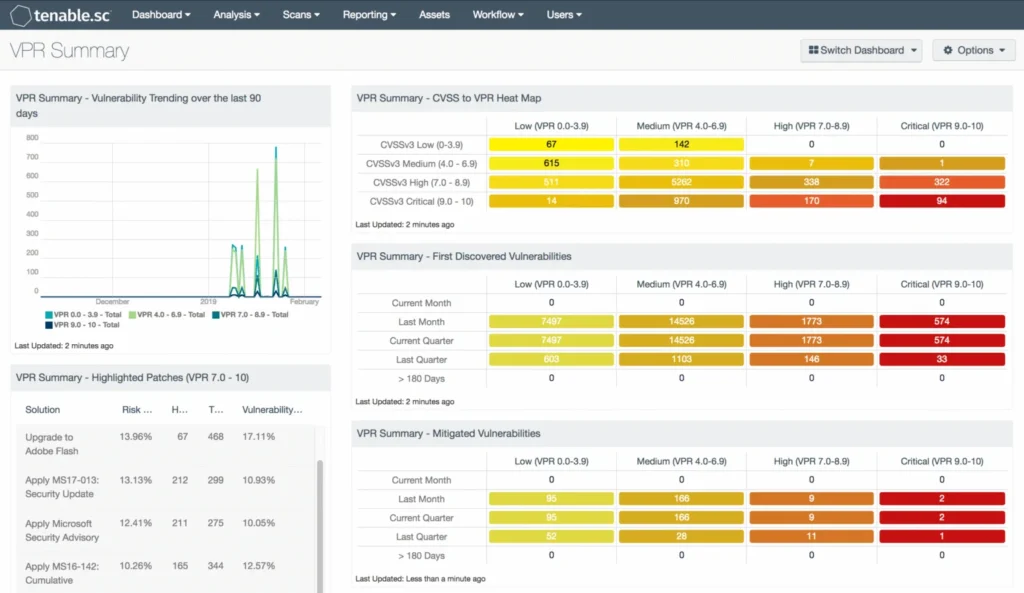
4️⃣ Risk-Based Vulnerability Prioritization (VPR) ⚠️
One of Tenable’s most powerful innovations is Vulnerability Priority Rating (VPR).
Instead of ranking vulnerabilities only by severity, Tenable analyzes:
- Exploit availability
- Threat intelligence
- Attacker behavior
- Asset importance
This produces a dynamic risk score showing which vulnerabilities attackers are most likely to exploit.
👉 Why this matters:
Security teams focus on real threats not theoretical ones saving time and resources.

5️⃣ Cloud Security Posture Management ☁️
As organizations move to cloud infrastructure, misconfigurations become a major risk.
Tenable scans cloud environments like AWS and Azure to detect:
- Publicly exposed storage
- Excess permissions
- Weak access controls
- Misconfigured services
👉 Why this matters:
Many modern breaches occur due to cloud misconfigurations not malware.
6️⃣ Web Application Scanning 🌐
Tenable also protects web apps and APIs through dynamic application security testing (DAST).
It detects issues such as:
- SQL injection
- Cross-site scripting (XSS)
- Authentication flaws
- Input validation risks
👉 Why this matters:
Web apps are public-facing making them prime attack targets.
7️⃣ Operational Technology (OT) Security 🏭
Tenable provides deep visibility into industrial and operational technology systems like:
- Manufacturing equipment
- Energy grids
- ICS networks
- Industrial controllers
These systems often run legacy software and can’t be patched easily.
👉 Why this matters:
Protecting OT infrastructure is critical for national and industrial security.
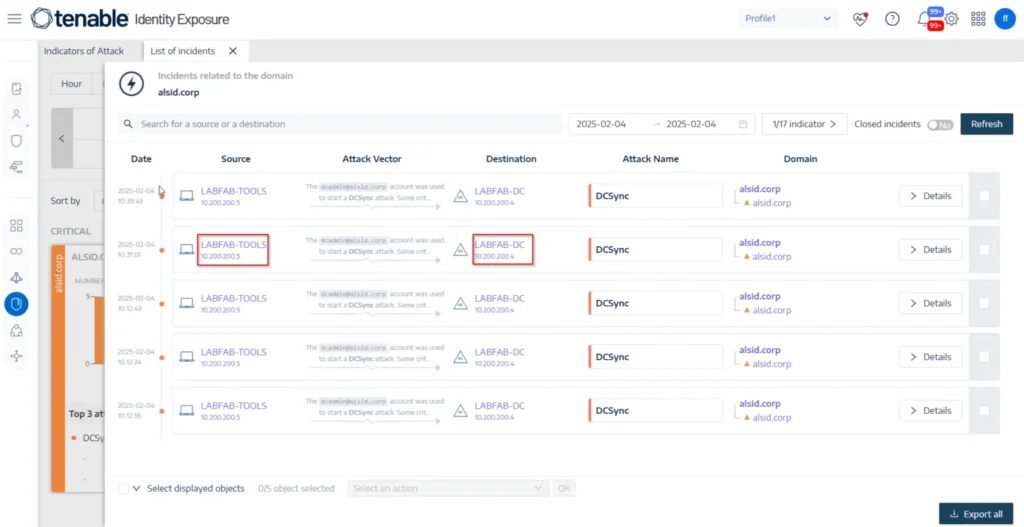
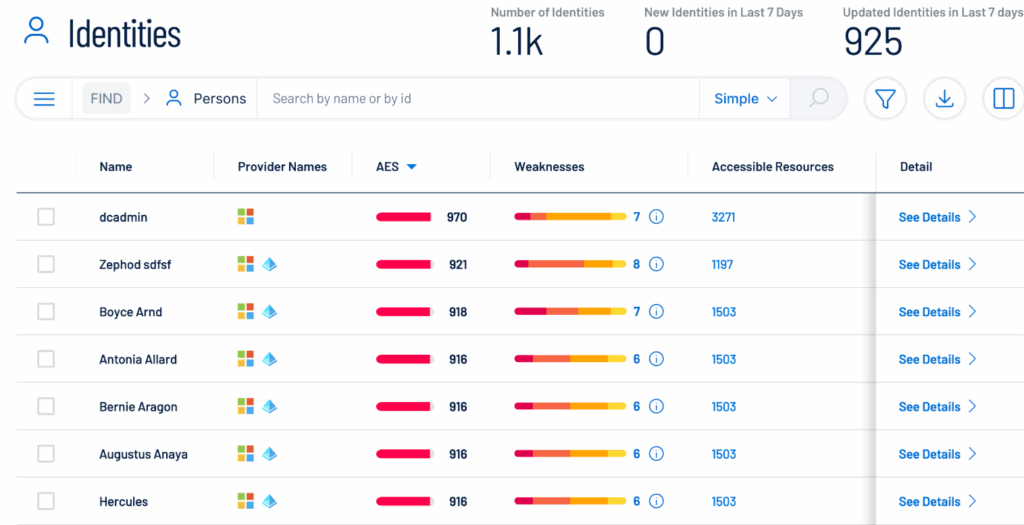
8️⃣ Identity Exposure Management 🧠
Identity risks are a growing attack vector.
Tenable identifies:
- Excess user privileges
- Misconfigured identity roles
- Risky access permissions
👉 Why this matters:
Attackers often exploit identity gaps instead of technical vulnerabilities.
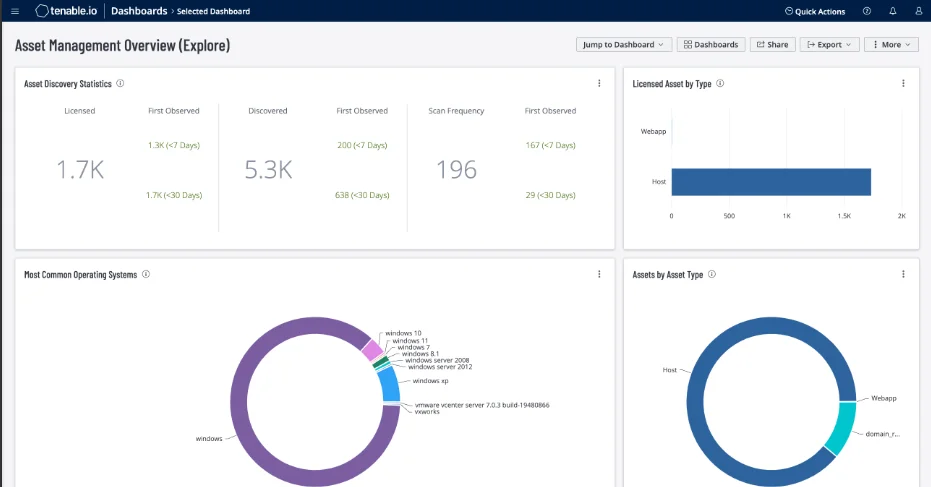
9️⃣ Advanced Dashboards & Reporting 📈
Tenable converts raw security data into visual dashboards that show:
- Risk trends
- Exposure scores
- Critical vulnerabilities
- Compliance posture
Reports can be customized for technical teams or executives.
👉 Why this matters:
Security insights become easier to understand and act on.
🔟 Integrations & Workflow Automation 🔗
Tenable integrates with enterprise tools like:
- SIEM platforms
- Ticketing systems
- DevOps pipelines
This allows vulnerabilities to automatically generate remediation workflows.
👉 Why this matters:
Detection alone isn’t enough automation speeds up response.
🧠 Final Feature Summary
In simple terms, Tenable provides:
✔ Detection → Finds vulnerabilities | ✔ Visibility → Discovers all assets | ✔ Prioritization → Ranks real risk | ✔ Analytics → Shows exposure trends | ✔ Automation → Speeds remediation
This combination makes Tenable a complete cyber exposure management platform, not just a scanner.
Tenable scans systems against thousands of known vulnerabilities, including actively exploited threats listed in the official Known Exploited Vulnerabilities Catalog maintained by CISA.
⚙️ How Tenable Works (Step-by-Step Process) 🔍🛡️
Tenable works like a security radar it finds your assets, scans them for weaknesses, tells you what’s most dangerous, and helps you fix it fast. Here’s the full flow in simple words 👇
✅ Step 1: Discover All Assets (Visibility First) 🖥️☁️
Tenable starts by identifying everything connected to your environment, such as:
- Endpoints (laptops/desktops)
- Servers
- Network devices
- Cloud workloads
- IoT / OT systems
👉 Why it matters:
If an asset is not visible, it becomes a hidden attack entry point. Asset discovery removes blind spots.
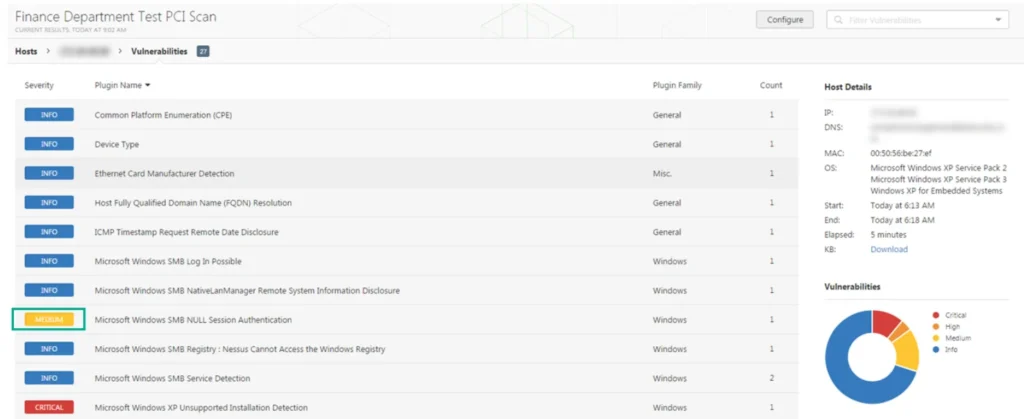
✅ Step 2: Run Vulnerability Scans (Find Weak Points) 🔍
Once assets are discovered, Tenable scans them to detect:
- CVEs (known vulnerabilities)
- Missing patches
- Misconfigurations
- Weak security settings
It uses a frequently updated vulnerability database, so detection stays current.
👉 Why it matters:
This is how Tenable finds risks before attackers do.
✅ Step 3: Analyze & Prioritize Risk (Fix What Matters First) ⚠️🧠
Tenable doesn’t just list issues it ranks them using:
- Exploit likelihood
- Threat intelligence
- Asset criticality
- VPR scoring (Vulnerability Priority Rating)
So instead of “10,000 issues,” you get a clear what to fix first list.
👉 Why it matters:
Teams save time and reduce real-world breach risk.
✅ Step 4: View Cyber Exposure (Big Picture Risk) 📊
With Tenable One, you get a unified exposure view combining:
- Vulnerabilities
- Cloud misconfigurations
- Identity exposure
- OT/IoT risk
- Web app risks
It shows your overall exposure score and key risk areas.
👉 Why it matters:
It gives leadership and security teams one clear “risk dashboard.”
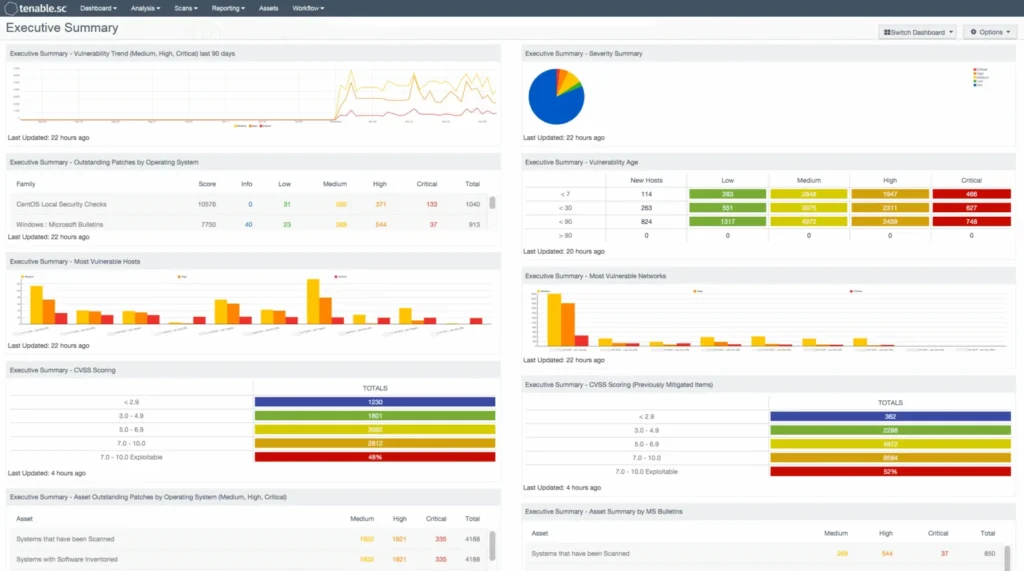
✅ Step 5: Generate Reports & Alerts (Stay In Control) 🚨📈
Tenable provides:
- Automated security reports
- Executive dashboards
- Compliance-ready reporting
- Real-time alerts when risk changes
👉 Why it matters:
You don’t just find issues — you track progress and prove improvements.
✅ Step 6: Remediate Faster with Integrations (Fix & Close the Loop) 🔗✅
Tenable integrates with tools like ticketing systems and SIEM platforms, so you can:
- Auto-create fix tickets
- Assign issues to teams
- Track remediation status
👉 Why it matters:
Security becomes actionable not just “reporting.”

🧩 Tenable Products Breakdown (Full Ecosystem Explained)
Tenable is not just one tool it’s a complete cybersecurity ecosystem designed to cover every layer of modern infrastructure. Each product focuses on a specific attack surface, but together they create a unified exposure management platform.
Let’s break down the main Tenable products in simple words 👇
🛡️ 1️⃣ Tenable Nessus (Vulnerability Scanner)
This is Tenable’s flagship and most recognized product.
Tenable Nessus is a vulnerability scanning tool that identifies security weaknesses across systems, applications, and networks. It scans for thousands of known vulnerabilities, missing patches, and configuration issues.

Key Capabilities:
- Deep vulnerability scanning
- Patch & configuration checks
- Compliance auditing
- Risk scoring insights
👉 Best for: Security professionals, pentesters, consultants, and IT teams who want accurate vulnerability detection.
💡 Nessus is often considered the industry standard for vulnerability scanning.
🧠 2️⃣ Tenable One (Unified Exposure Management Platform)
Tenable One is the company’s all-in-one cyber exposure platform.
Instead of managing vulnerabilities, identities, cloud risks, and OT exposures separately, Tenable One combines everything into a single dashboard.
What It Unifies:
- Vulnerability data
- Identity exposure
- Cloud misconfigurations
- Web app risks
- OT & IoT visibility
👉 Best for: Enterprises needing a centralized view of organizational cyber risk.
💡 It replaces multiple security tools with one unified risk intelligence layer.
☁️ 3️⃣ Tenable Cloud Security
As businesses move to cloud infrastructure, Tenable provides dedicated cloud protection.
This product focuses on identifying misconfigurations, permission risks, and exposed services across platforms like AWS and Azure.

Key Capabilities:
- Cloud posture management
- Permission risk detection
- Infrastructure misconfiguration alerts
- Cloud asset visibility
👉 Best for: Cloud-native organizations and DevOps teams.
💡 Most modern breaches originate from cloud misconfigurations making this tool critical.
🌐 4️⃣ Tenable Web App Scanning
This solution focuses on protecting web applications and APIs through dynamic security testing.
It simulates real attack scenarios to detect vulnerabilities such as:
- SQL Injection
- Cross-site scripting (XSS)
- Authentication flaws
- Input validation weaknesses
👉 Best for: SaaS companies, web platforms, and eCommerce sites.
💡 Since web apps are public-facing, they’re among the most targeted assets.

🏭 5️⃣ Tenable OT Security
Operational Technology environments require specialized security and Tenable provides that through OT Security.
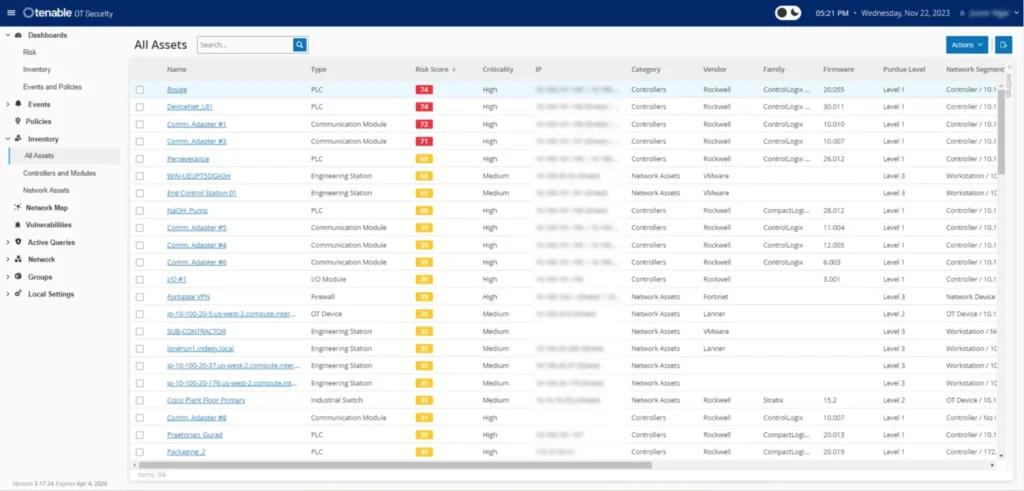
It monitors industrial systems such as:
- Manufacturing equipment
- Industrial control systems (ICS)
- Energy & utility networks
- Critical infrastructure
👉 Best for: Industrial, manufacturing, and infrastructure organizations.
💡 OT systems often run legacy tech, making visibility more important than patching.
🧠 6️⃣ Identity Exposure (Identity Security)
Identity risks are a growing attack vector, and Tenable addresses this through identity exposure management.
It identifies:
- Excess privileges
- Risky identity configurations
- Access control gaps
👉 Best for: Organizations using hybrid identity environments.
💡 Many breaches today start with compromised credentials not malware.
💰 Tenable Pricing Plans
Tenable offers multiple pricing models depending on the product, features, and deployment scope. Instead of a one-size plan, pricing is segmented based on scanning depth, asset coverage, and advanced exposure capabilities.
Below is a simplified breakdown based on the plans you shared 👇
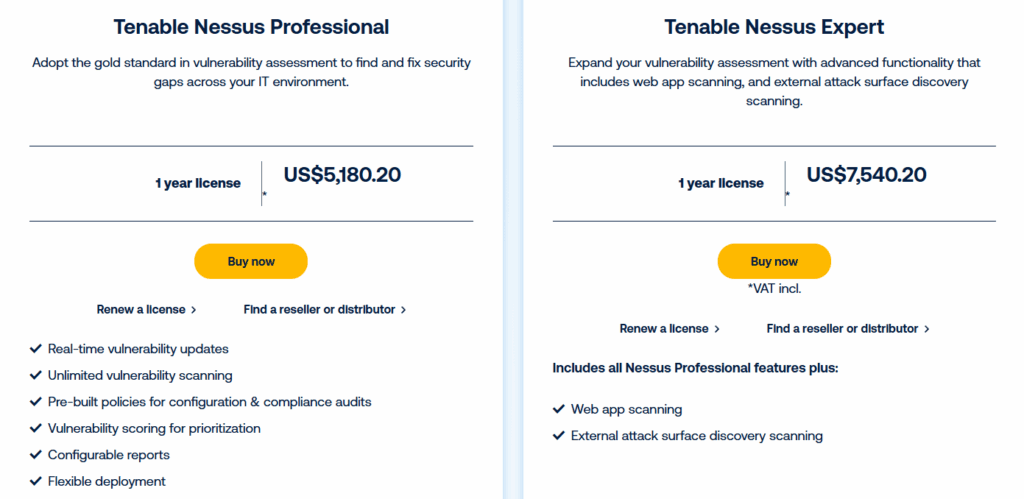
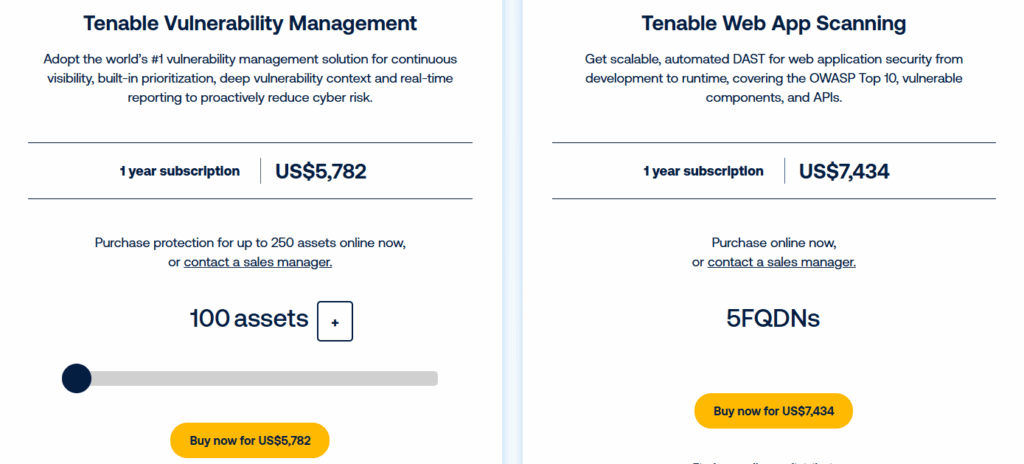
🧾 Tenable Pricing Comparison Table
| Plan / Product | License Type | Pricing Model | Key Features Included |
|---|---|---|---|
| Nessus Professional | 1-Year License | $431.68 / month | Unlimited scans, real-time vulnerability updates, compliance policies |
| Nessus Expert | 1-Year License | $628.35 / month | Includes Pro features + Web App Scanning + External Attack Surface Discovery |
| Vulnerability Management | Annual Subscription | $57.82 / asset / year | Continuous monitoring, asset prioritization, exposure analytics |
| Web App Scanning | Annual Subscription | $7,434 / year | DAST scanning, OWASP coverage, API vulnerability detection |
If Tenable fits your security requirements, it’s smart to check whether any active Tenable discount is available before choosing a subscription plan.
⚖️ Tenable Pros & Cons (Side-by-Side Comparison)
| ✅ Pros | ❌ Cons |
|---|---|
| Industry-trusted vulnerability scanner (Nessus) 🛡️ | Higher pricing compared to basic scanners 💰 |
| Risk-based prioritization with VPR scoring ⚠️ | Learning curve for advanced dashboards 📘 |
| Complete exposure visibility across IT, cloud & OT 📊 | Enterprise modules cost extra |
| Continuous asset discovery & monitoring 🔍 | Asset-based pricing can scale quickly |
| Highly scalable for enterprise environments 🏢 | Not ideal for very small teams |
| Strong compliance & audit reporting 📋 | Setup may require security expertise |
| Flexible deployment (cloud, on-prem, hybrid) ☁️ | Advanced features locked in higher tiers |
🧠 Quick User Insight
If your priority is accuracy + enterprise security visibility → Pros outweigh cons.
If your priority is budget-only scanning → Cons may matter more.
🎯 Who Should Use Tenable? (And Who Should Avoid It)
✅ Who Should Use Tenable
Security Professionals & Pentesters : Nessus delivers deep, accurate vulnerability scanning ideal for testing and risk assessment. 🔍
Enterprises & Large IT Environments : Perfect for organizations managing large infrastructures needing centralized exposure visibility. 🏢
IT & Security Teams : Helps automate discovery, prioritize threats, and manage remediation efficiently.
Cloud & Hybrid Businesses : Strong cloud posture monitoring and misconfiguration detection. ☁️
Compliance-Focused Industries : Useful for audit reporting and regulatory security frameworks. 📋

❌ Who Should Avoid Tenable
Small Businesses / Solo Users : May feel expensive and feature-heavy for limited environments.
Budget-First Buyers : Lower-cost scanners exist (with fewer capabilities).
Non-Technical Users : Advanced dashboards require some cybersecurity knowledge.
One-Time Scan Needs : Subscription pricing suits continuous monitoring, not temporary use.
Tenable vs Competitors 🆚
When evaluating Tenable, most users compare it with platforms like Qualys and Rapid7. While all three focus on vulnerability management, their approach and strengths differ.
Tenable vs Qualys
Tenable is often preferred for its easier deployment and strong hybrid environment support. It works well across on-prem and cloud infrastructures. Qualys, on the other hand, is more cloud-native and enterprise-heavy, which may require more setup complexity.

👉 If you want flexibility → Tenable fits better.
👉 If you’re fully cloud-focused → Qualys may appeal more.
Tenable vs Rapid7
Tenable specializes deeply in vulnerability and exposure management. Rapid7 expands further into threat detection and SIEM capabilities, making it broader but also more complex.
👉 If your focus is vulnerability prioritization → Tenable leads.
👉 If you want SOC + detection tools → Rapid7 offers more coverage.
🏁 Is Tenable Worth It? (Final Verdict)
Yes, Tenable is worth it if vulnerability management and cyber exposure visibility are serious priorities for your organization.
It goes beyond basic scanning by combining risk prioritization, asset discovery, and exposure analytics into one ecosystem. This makes it especially valuable for enterprises, security teams, and compliance-driven industries. 🔐
However, for very small businesses or users needing only occasional scans, Tenable may feel feature-heavy and cost-intensive compared to simpler tools.
👉 Final Take:
- Need enterprise-grade security visibility → Tenable is a strong choice
- Need budget or short-term scanning → Consider lighter alternatives

Overall, Tenable stands out as a reliable, scalable, and intelligence-driven cybersecurity platform trusted across industries. 🚀
❓ Frequently Asked Questions
1️⃣ Does Tenable require internet access to run scans? 🌐
Not always. Nessus can run internal scans without internet, but plugin updates and threat intelligence require connectivity.
2️⃣ How accurate are Tenable vulnerability scans? 🎯
Tenable is known for high detection accuracy, thanks to its large and frequently updated vulnerability plugin database.
3️⃣ Can Tenable scan cloud and on-prem systems together? ☁️
Yes, Tenable supports hybrid environments and provides unified visibility across cloud and on-prem assets.
4️⃣ Does Tenable provide remediation guidance? 🛠️
Yes, scan results include fix recommendations, patch details, and configuration guidance.
5️⃣ How often should Tenable scans be run? ⏱️
Most organizations run continuous or weekly scans to stay updated on new vulnerabilities.