Modern supply chains no longer run only on trucks, warehouses, and people 🚚🏭
They run on data and a huge part of that data comes from IoT devices like GPS trackers, temperature sensors, RFID scanners, and smart monitoring systems 📡.
These devices quietly power real-time shipment tracking, delivery ETAs, condition monitoring, and automated alerts. When they work, everything feels smooth and predictable.
But when they are unsecured or compromised, the impact is immediate wrong locations, delayed shipments, missing inventory, and confused teams 😟.

What makes IoT security especially dangerous is that failures don’t look like “cyber attacks” at first. They look like operational problems late trucks, bad data, broken visibility, and constant firefighting.
This is why unsecured IoT devices are no longer just a technical risk they are a direct threat to supply chain operations and trust.
In this article, we’ll break down how unsecured IoT devices disrupt supply chain operations, what actually goes wrong on the ground, and why protecting IoT infrastructure is essential for keeping logistics predictable and reliable 🔐📦.
🌐 The IoT Revolution in Modern Supply Chains
The supply chain industry has undergone a massive transformation over the past decade. Gone are the days when tracking meant phone calls and paperwork. Today, IoT devices are the backbone of modern logistics silently working 24/7 to keep goods moving across the globe. 📦
From GPS trackers on shipping containers to temperature sensors in refrigerated trucks, from RFID scanners in warehouses to smart locks on cargo doors these connected devices generate millions of data points every single day. They tell us where shipments are, what condition they’re in, and when they’ll arrive.
This real-time visibility isn’t just convenient it’s become a competitive necessity. Companies that can track inventory down to the pallet level, predict delays before they happen, and automate warehouse operations are simply outperforming those that can’t. 📈
But here’s the catch: every IoT device is also a potential entry point for cyberattacks. And most companies don’t realize how exposed they actually are.
🔹The Scale of IoT in Logistics
Let’s put this in perspective:
- 🚛 A single logistics company might have 10,000+ GPS trackers across its fleet
- 📦 Modern warehouses deploy hundreds of RFID readers and sensors
- 🌡️ Cold chain operations use thousands of temperature monitors for compliance
- 🔒 Smart locks and access control systems secure every loading dock and storage area
Each of these devices connects to networks, transmits data, and can be remotely accessed. Each one is a potential vulnerability.
📍 Why IoT Devices Are Critical to Supply Chain Visibility
Let’s break down why these devices matter so much to modern operations:
1️⃣ Real-Time Tracking 🗺️
GPS trackers on trucks, ships, and containers provide live location updates. Logistics managers can see exactly where every shipment is at any moment, which means better planning and faster response to disruptions.
Without this, you’re back to calling drivers every few hours and hoping they answer.
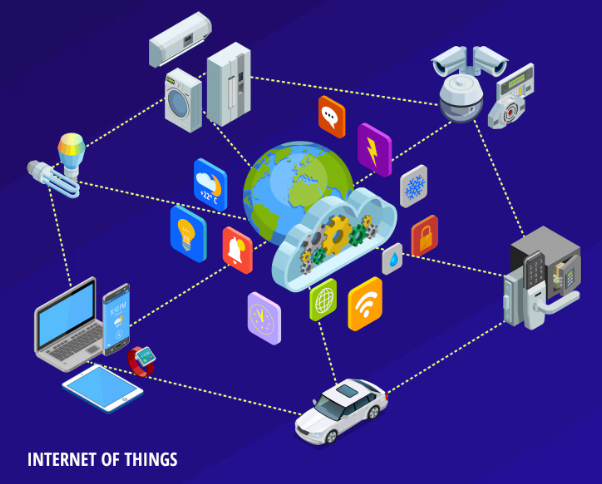
2️⃣ Condition Monitoring 🌡️
Temperature sensors ensure cold chain integrity for pharmaceuticals and food. Shock sensors detect rough handling. Humidity monitors protect sensitive electronics. One sensor failure could mean millions in spoiled inventory.
3️⃣ Automated ETAs ⏱️
IoT devices feed data into supply chain platforms that calculate accurate delivery windows. Customers expect precision, and these sensors make it possible. The “it’ll arrive sometime next week” era is over.
4️⃣ Warehouse Automation 🏭
RFID scanners, barcode readers, and smart conveyor systems speed up receiving, picking, and shipping. Modern warehouses process thousands of items per hour thanks to IoT connectivity.
5️⃣ Proof of Delivery ✅
Digital signatures, photo capture devices, and geofencing technology create an audit trail that protects against disputes and fraud.
6️⃣ The Bottom Line
Without IoT devices, supply chains would be flying blind. They’ve become so embedded in operations that most companies can’t function without them anymore. This dependency is exactly what makes their security so critical.
🔓 The Hidden Vulnerability: Unsecured IoT Endpoints
Here’s the uncomfortable truth: most companies secure their laptops and servers, but completely ignore their IoT devices. 🚨
🔹Why Does This Happen?
They’re invisible to IT teams 👻 IoT devices often get deployed by operations or logistics teams, not IT. They’re purchased through procurement, installed by vendors, and never show up on the IT asset register.
Your IT security team might be running sophisticated threat detection on servers while completely unaware that there are 500 connected sensors in the warehouse.
“Set and Forget” mentality 😴 Once a GPS tracker is installed on a truck, nobody thinks about it again until it stops working. Security updates? Never happen. Password changes? What password?
Assumed isolation 🏝️ Many people think, “It’s just a sensor, what harm can it do?” But these devices connect to networks, send data to cloud platforms, and often have remote management capabilities.
Legacy equipment 📟 Some IoT devices in warehouses and distribution centers are 5-10 years old, running outdated firmware with known vulnerabilities that will never be patched because the manufacturer discontinued the product line.
Vendor responsibility confusion 🤷 Companies assume the device manufacturer handles security. Manufacturers assume the customer does. Nobody actually does.
🔹The Blind Spot Effect
This creates a massive blind spot. While your IT team is busy securing email and databases, there are dozens or hundreds of connected devices humming along in trucks, warehouses, and loading docks completely unmonitored and unprotected.
And attackers know this. In fact, IoT devices are often the easiest way into a corporate network.
Many IoT devices are deployed quickly and with minimal protection, exposing endpoints that rarely receive patches or monitoring. For a deeper breakdown of what IoT security encompasses including real risks and examples see “What Is IoT Security? Risks, Examples, and Solutions.”
⚠️ Common IoT Security Risks in Supply Chain Operations
Let’s get specific about what can go wrong. These aren’t theoretical risks they’re actively being exploited right now:
| Risk Type | What It Means | Why It’s Dangerous |
|---|---|---|
| 🔑 Default Credentials | Devices ship with admin/admin123 | Attackers have databases of every default password |
| 🔧 Unpatched Firmware | Known vulnerabilities never fixed | Exploits are publicly available online |
| 🌐 Internet-Exposed Devices | Public IP addresses, no VPN | Automated scanners find them in minutes |
| 🔐 Weak Authentication | No 2FA, simple passwords | Easy brute-force attacks |
| 🏢 Unsegmented Networks | IoT shares network with servers | One sensor = entire network access |
| 🔨 Physical Tampering | Devices in accessible locations | Direct hardware manipulation possible |

🔹Deep Dive: The Default Credential Problem
That GPS tracker shipped with username “admin” and password “admin123.” The warehouse scanner came with a hardcoded password printed in the manual. Most companies never change these, and attackers have lists of every default credential for every IoT device ever made.
Tools like Shodan (the “search engine for IoT devices”) make it trivial to find exposed devices. An attacker can search for a specific model of RFID reader, find thousands of them online, and try the default credentials. Success rate? Shockingly high. 😱
🔹The Unpatched Firmware Crisis
A vulnerability gets discovered in a popular temperature sensor. The manufacturer releases a patch. But who’s responsible for applying it?
- The logistics team doesn’t know it exists
- The IT team doesn’t know they have these devices
- The vendor who installed them isn’t contracted for ongoing maintenance
- The device keeps running for years with a known exploit
🔹Internet Exposure Reality
To enable remote monitoring, many IoT devices are accessible from the internet. Sometimes they’re behind a VPN (good), but often they’re just sitting there with a public IP address (very bad), waiting to be found by automated scanners that probe the entire internet 24/7.
💥 How Compromised IoT Devices Disrupt Operations
When an IoT device gets hacked, the damage isn’t always obvious. There’s no ransom note on your screen. No locked files. Instead, you get silent operational chaos:

1️⃣ Wrong Location Data 📍❌
Attackers manipulate GPS trackers to show fake locations. A truck that’s actually stuck at a border crossing appears to be on schedule. By the time you realize the truth, it’s too late to reroute or notify customers.
Your customer service team is telling clients “Your shipment will arrive in 2 hours” based on GPS data that’s completely false.
2️⃣ Delayed Shipments ⏰
Ransomware hits a warehouse automation system. Suddenly, RFID scanners won’t read, conveyor belts won’t move, and the entire facility grinds to a halt. Hours of downtime means missed delivery windows and penalty fees.
One compromised IoT controller can shut down operations worth millions per day.
3️⃣ False Alerts 🚨
Temperature sensors get compromised and send normal readings even when refrigeration fails. By the time someone notices, an entire shipment of vaccines or fresh food is ruined.
Or worse: sensors trigger constant false alarms, and your team learns to ignore them. Then a real problem happens, and nobody responds.
4️⃣ Lost Visibility 👁️
Hackers disable tracking devices on high-value cargo. The shipment goes dark for days. You don’t know if it’s been stolen, rerouted, or sitting in the wrong warehouse.
5️⃣ Cascading Failures 🌊
One compromised sensor feeds bad data into your supply chain management system. That triggers:
- ❌ Incorrect inventory counts
- ❌ Wrong reorder quantities
- ❌ Misallocated resources across multiple facilities
- ❌ Poor demand forecasting
- ❌ Customer delivery failures

6️⃣ Customer Trust Erosion
When deliveries are consistently late and you can’t explain why, customers lose confidence. They don’t know it’s because your IoT infrastructure is compromised they just know you can’t deliver on your promises.
The scary part? You might not even know it’s happening. Unlike a ransomware attack that locks your screen, IoT compromises can run silently for weeks or months, slowly degrading your operations.
Cyber attackers often target interdependent systems and when supply chain tech and associated devices are compromised, the effects ripple across operations. For examples of how supply chain attacks have caused real harm and practical defensive strategies, see “Supply Chain Attacks: 7 Examples and 4 Defensive Strategies.”
💰 The Real Cost of IoT-Related Supply Chain Breaches
Let’s talk numbers, because the impact is bigger than most people think:
| Cost Category | Typical Range | Real-World Example |
|---|---|---|
| 🏭 Warehouse Downtime | $100K – $1M per day | RFID system ransomware halts operations |
| 🧊 Spoiled Inventory | $500K – $5M per incident | Temperature sensor compromise ruins cold chain |
| 📋 SLA Penalties | $50K – $500K per breach | Late deliveries trigger contract penalties |
| 👥 Customer Churn | 15-30% revenue loss | Major clients switch to competitors |
| 🔍 Incident Response | $200K – $800K | Forensics, remediation, device replacement |
| ⚖️ Regulatory Fines | $500K – $10M+ | Pharmaceutical tracking violations |
| 📰 Reputational Damage | Immeasurable | Brand trust takes years to rebuild |
🔹The Hidden Costs
Beyond direct financial losses, consider:
Emergency firefighting 🚒 — Your best people drop everything to fix the crisis. Normal operations suffer. Strategic projects get delayed.
Insurance premium increases 📈 — After a breach, cyber insurance costs skyrocket. Some companies become uninsurable.
Audit and compliance overhead 📊 — Post-incident, regulators want detailed reports. Customers demand security audits. Every response costs time and money.
Lost competitive advantage 🏆 — While you’re recovering, competitors are innovating. The gap widens.
🔹Real Cost Example
A mid-sized logistics company experienced a GPS tracker compromise that went undetected for 3 weeks:
- 23 shipments misdirected → $1.2M in lost/stolen goods
- 47 late deliveries → $280K in SLA penalties
- Customer compensation → $150K
- Incident response and remediation → $320K
- Insurance deductible → $100K
- Total direct cost: $2.05M
Indirect costs (customer churn, reputation, lost opportunities): Estimated $3-5M over 18 months
The cost of proper IoT security monitoring that would have prevented this? About $75K annually.
The ROI is obvious.
Industrial control systems are often connected to unsecured IoT endpoints, increasing operational risk across warehouses and transportation networks. Discover how unsecured IoT devices disrupt supply chain logistics.
🔍 Identifying IoT Exposure in Supply Chain Infrastructure
The first step to securing IoT devices is actually knowing what you have. This sounds basic, but it’s where most companies fail.
1. The Discovery Challenge
Your network team might know about:
- ✅ WiFi access points
- ✅ Security cameras
- ✅ Office computers and servers
But do they know about:
- ❓ The GPS trackers communicating via cellular networks
- ❓ The Bluetooth-enabled pallet sensors in the warehouse
- ❓ The RFID readers connected through a vendor’s managed service
- ❓ The temperature loggers that only transmit data once a day
- ❓ The smart locks installed by the facilities team last month
Traditional IT security tools weren’t built for this. They scan for computers and servers, not for low-power sensors and specialized logistics hardware.

2. Modern Exposure Management
This is where exposure management platforms come in. Instead of just looking for known devices, they can identify anything that’s communicating on your network even devices you didn’t know existed.
They map out your entire attack surface:
🔍 Asset Discovery
- Every device, known or unknown
- Communication patterns and protocols
- Network locations and connections
🎯 Vulnerability Assessment
- Which devices are internet-facing
- Which ones are running outdated firmware
- Which ones have default credentials
- Which ones have known CVEs (Common Vulnerabilities and Exposures)
⚡ Risk Prioritization
- Critical devices (cold chain sensors, access controls)
- High-exposure devices (internet-facing, default passwords)
- Low-risk devices that can wait for scheduled maintenance

3. The Tenable Approach
Platforms like Tenable specialize in continuous exposure management across diverse environments including IoT and OT (operational technology) devices that traditional security tools miss.
Rather than periodic scans that disrupt operations, they provide:
- 👁️ Passive monitoring that doesn’t interfere with sensor operations
- 🗺️ Complete asset inventory across IT, IoT, and OT
- 📊 Risk-based prioritization so you focus on what matters most
- 🔄 Continuous visibility as new devices get added
The goal isn’t perfection it’s visibility. Once you know what’s out there, you can prioritize. A GPS tracker on a delivery van is lower risk than an RFID system that controls access to a pharmaceutical warehouse.
This kind of continuous discovery means that when operations teams install new sensors or when vendors add tracking devices, you actually know about it before attackers do.
Monitoring IoT Risk Without Breaking Operations
A common misconception in supply chain environments is that monitoring IoT risk inevitably slows operations down.
This belief usually comes from experience with traditional security controls that demand shutdowns, intrusive scans, or manual audits. In logistics, where uptime is non-negotiable, such approaches simply don’t scale.
Effective IoT risk monitoring works differently. It focuses on continuous awareness rather than periodic intervention.
Instead of stopping devices to inspect them, organizations monitor communication patterns, exposure levels, and behavioral anomalies while operations continue uninterrupted.
The objective is not to eliminate every vulnerability immediately, but to understand which risks matter operationally.
A temperature sensor in a low-value shipment does not carry the same weight as a GPS tracker feeding real-time location data into routing and customer systems. Prioritization based on business impact allows teams to act intelligently without disrupting flow.
When monitoring is designed to support operations rather than control them, security becomes an enabler of stability not a source of friction.
Integrating IoT Security with Supply Chain Platforms
Now let’s connect the dots between security and operations. Your supply chain management platform relies on clean, accurate data from IoT devices. When those devices are compromised, bad data flows into your operational systems.
The Data Integrity Problem
Take a platform like ShipChain SCM it aggregates data from multiple sources to give you end-to-end supply chain visibility:
- 📍 GPS trackers on vehicles and containers
- 🌡️ Temperature and condition sensors
- 📦 Warehouse RFID and barcode systems
- 🚢 Carrier integration APIs
- ⛓️ Blockchain-based verification for custody and authenticity
But here’s what happens when IoT security fails:

Scenario 1: Garbage In, Garbage Out 🗑️
If a compromised GPS tracker feeds fake location data into ShipChain:
- ❌ Your ETAs will be wrong
- ❌ Your customers get incorrect delivery notifications
- ❌ Your warehouse staff prepare to receive shipments that haven’t actually arrived
- ❌ Your entire operational plan is based on lies
Scenario 2: Broken Automation ⚙️
Modern supply chain platforms use IoT data to trigger automated workflows:
- ✅ When shipment crosses geofence → send notification
- ✅ When temperature exceeds threshold → alert logistics manager
- ✅ When RFID confirms receipt → update inventory
- ✅ When smart lock opens → log access event
Compromised sensors can:
- 🚨 Trigger false alerts that waste time
- 🔕 Suppress real alerts when problems occur
- 🔄 Create automation loops that amplify issues
- 💥 Cascade failures across connected systems

Scenario 3: Lost Audit Trail 📋
Blockchain-based supply chain platforms like ShipChain create immutable records of:
- 📦 Custody transfers
- 📍 Location history
- 🌡️ Condition monitoring
- ✅ Verification checkpoints
But if the IoT devices feeding that data are compromised, you’re just creating a permanent record of lies. The blockchain doesn’t make bad data good it just makes it unchangeable.
🔹Real-World Integration
When ShipChain shows you that a shipment is delayed, you need confidence that the underlying IoT data is trustworthy:
- Device verification — Is the GPS tracker authenticated and tamper-free?
- Data validation — Does the location data make logical sense?
- Cross-reference — Do other data points (carrier check-ins, port scans) confirm the location?
- Behavioral analysis — Is this device behaving normally or showing signs of compromise?
Security isn’t separate from operations it enables operations.
You can’t have reliable supply chain visibility without secure IoT infrastructure. They’re two sides of the same coin.
Case Scenario – Preventing GPS Tracker Manipulation
Consider a high-value shipment moving across multiple regions. According to the GPS tracker, everything looks normal steady movement, predictable stops, on-time arrival projected.
But in the background, subtle anomalies appear:
- The device begins communicating through an unusual network
- Location updates remain consistent even when movement patterns should vary
- The signal behavior no longer matches historical routes
Instead of waiting for a missed delivery, the operations team flags the shipment for verification. The data stream is isolated, alternative tracking is used, and downstream systems are alerted to treat the ETA as provisional.
The shipment arrives with a delay but without chaos.
No customer escalation.
No inventory misallocation.
No reactive firefighting.
The lesson is simple: early skepticism of IoT data prevents late-stage operational failure. The win wasn’t technical sophistication it was timely visibility and controlled response.
Future-Proofing IoT-Driven Supply Chain Operations
Supply chains are becoming more automated, more connected, and more dependent on machine-generated data. This trajectory is irreversible. What remains optional for now is how prepared organizations are to manage the risks that come with it.
Future-proofing IoT-driven operations does not mean predicting every threat. It means building systems that assume imperfection:
- Data may be delayed
- Signals may be wrong
- Devices may fail or be manipulated
Resilient supply chains are not those with flawless visibility, but those with controlled uncertainty. They know when to trust automation and when to pause, verify, or override it.
In the long term, competitive advantage will not come from who has the most IoT devices but from who maintains operational control when IoT data cannot be fully trusted.
That is where visibility, preparedness, and disciplined execution converge.
“Related Article”
- How ShipChain Accounting & Tenable Build Finance Confidence
- How Do Cyber Attacks Affect Supply Chain Operations?
FAQs
❓ Are IoT devices really a security risk in supply chain operations?
Yes. IoT devices often run unattended, use outdated firmware, and connect directly to logistics systems. When unsecured, they can silently feed incorrect data or disrupt real-time visibility without triggering obvious alerts.
❓ How can compromised IoT devices affect day-to-day logistics?
They can cause wrong location updates, false alerts, delayed shipments, and poor decision-making. Teams may react to bad data, leading to reroutes, missed ETAs, and increased operational costs.
❓ Does monitoring IoT security slow down supply chain operations?
No, when done correctly. Effective IoT risk monitoring is lightweight and continuous, designed to detect exposure and unusual behavior without interrupting tracking, routing, or daily workflows.
❓ What’s the first step to reducing IoT-related supply chain disruptions?
The first step is visibility. Teams need to know which IoT devices are connected, which ones are exposed or outdated, and which operations depend on them. You can’t protect or manage what you can’t see.